
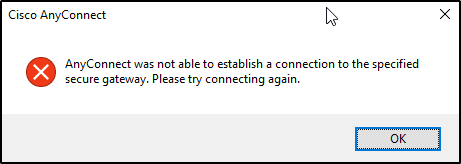
[Solved] how to resolve the Cisco VPN error message “Anyconnect was not able to establish a connection to the secure gateway. Please try connecting again.
[solved] how to resolve the Cisco VPN error message “Anyconnect was not able to establish a connection to the secure gateway. Please try connecting again”.
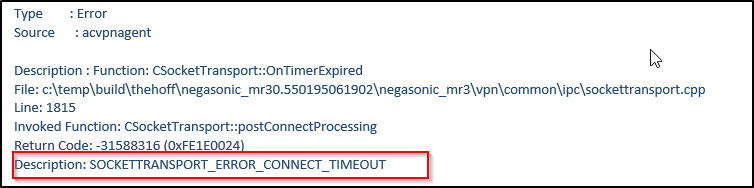
You can also the following error in the Cisco Anyconnect event logs
AnyConnect VPN dropping connection after few minutes and you can see in the ASA logs it says user requested.
The main issue is the user ISP firewall in the way blocking UDP 443.
Background Information from the Cisco site
Types of Tunnels
There are two methods used in order to connect an AnyConnect session:
- Via the Portal (Clientless)
- Via the Standalone Application
Based on the way you connect, you create three different tunnels (sessions) on the ASA, each one with a specific purpose:
- Clientless or Parent-Tunnel: This is the main session that is created in the negotiation in order to set up the session token that is necessary in case a reconnect is needed due to network connectivity issues or hibernation. Based on the connection mechanism, the Cisco Adaptive Security Appliance (ASA) lists the session as Clientless (Weblaunch via the Portal) or Parent (Standalone AnyConnect).
Note: The AnyConnect-Parent represents the session when the client is not actively connected. Effectively, it works similar to a cookie, in that it is a database entry on the ASA that maps to the connection from a particular client. If the client shuts down or sleeps, the tunnels (IPsec/Internet Key Exchange (IKE)/ Transport Layer Security (TLS)/Datagram Transport Layer Security (DTLS) protocols) are torn down, but the Parent remains until the idle timer or maximum connect time takes effect. This allows the user to reconnect without reauthenticating.Secure Sockets Layer (SSL)-Tunnel: The SSL connection is established first, and data is passed over this connection while it attempts to establish a DTLS connection. Once the DTLS connection is established, the client sends the packets via the DTLS connection instead of via the SSL connection. Control packets, on the other hand, always go over the SSL connection. - DTLS-Tunnel: When the DTLS-Tunnel is fully established, all data moves to the DTLS-tunnel, and the SSL-Tunnel is only used for occasional control channel traffic. If something happens to User Datagram Protocol (UDP), the DTLS-Tunnel is torn down and all data passes through the SSL-Tunnel again.
Below is the error message that you get, however most likely this is due ASA firewall sending a TCP reset, since first it authenticates the users and then sends a reset which drops the connection.
The second error message is “The vpn client failed to establish a connection”
It is always best practice to eliminate the user side by either restarting the PC or restarting the Cisco Anyconnect services to be sure that this is not related to the client.
Few Things to test before you start looking in ASA
- Reboot the computer
- disable the antivirus and connect again
- Right click the Anyconnect icon and choose repair.
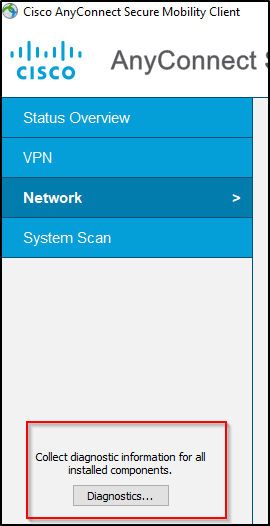
- Collect the Anyconnect DART bundle which has lots of information.
- Additionally, check that the ICS service is not running.
- Make sure DHCP is assigning addresses if you are using a DHCP server
- Select the Start button and then select Run.
- Type: services.msc and press ENTER on your keyboard.
- Find Internet Connection Sharing (ICS) and then stop the service.
- Change the Startup Type to Disabled and then reboot the computer.
If the above does not work then you will need to log in and check to see if it is the ASA that is dropping the connection because the connection is not coming as DTLS. The issue may then related to “DTLS”
The simple solution this is to disable DTLS on the Tunnel group.
You can do so by going to your ASA.


